
Discussions of wireless security increasingly reference very high radio frequencies, often above 7 GHz and extending into what are commonly called millimeter-wave frequencies. These frequencies also appear in discussions of satellite internet services and satellite phones, which can create the impression that attackers could easily exploit them to bypass traditional networks or monitoring tools.
In practice, wireless signals at these higher frequencies rarely pose a meaningful risk in real-world environments. Physical limits, environmental factors, and operational complexity make them poor choices for covert or reliable compromise. Understanding these constraints clarifies where wireless security efforts deliver the most significant value.
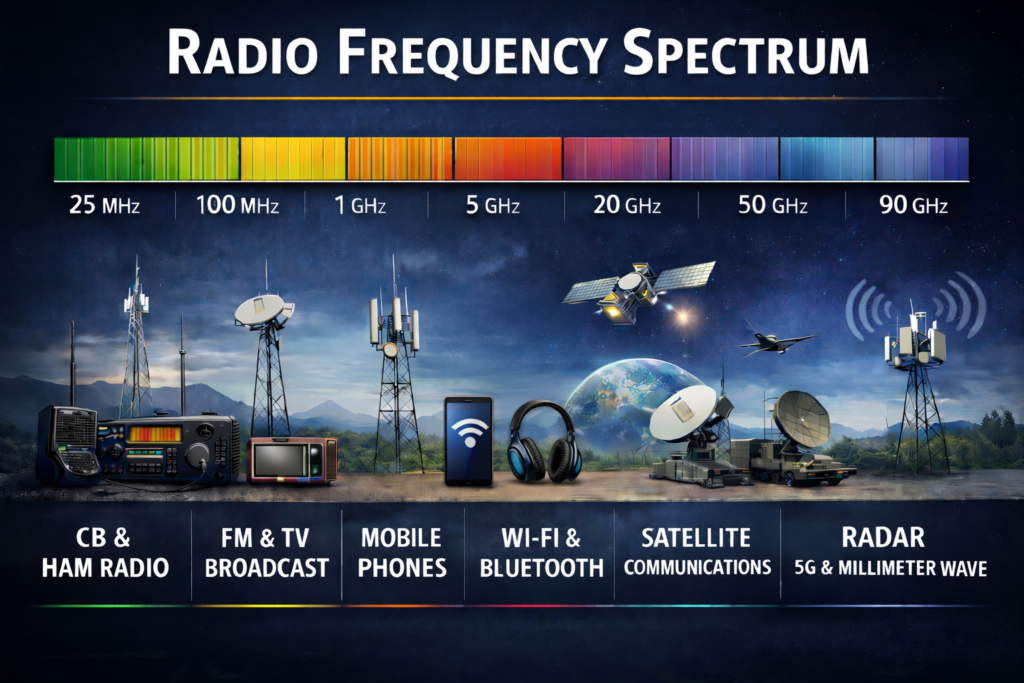
Figure 1 provides a general overview of the RF frequency spectrum from 25 MHz to 100 GHz and the types of communication that typically occur at each frequency range. Actual frequency allocations are more complex.
What Makes a Wireless Threat Viable
A viable wireless threat must operate consistently, remain undetectable, and require minimal effort. Most real-world attackers rely on technologies that operate indoors, pass through walls, and use inexpensive, readily available equipment.
Wireless technologies operating below 7 GHz meet these requirements. They provide stable indoor coverage, support longer-range connectivity, and operate inside everyday wireless devices, including Wi-Fi, mobile phones, and other connected devices. This combination makes them attractive to attackers and difficult to distinguish from everyday use.
Higher-frequency technologies lack many of these advantages. While they may support high data rates under ideal conditions, they struggle in everyday environments.
How Higher Frequencies Change Signal Behavior
As wireless signals move to higher frequencies, they decay more rapidly and cannot form links over reasonable distances without beamforming. It’s also more challenging and expensive to generate signals at these frequencies, and to produce them with significant power is very difficult. Even across a single room, signal quality can degrade significantly.
Walls, ceilings, doors, and windows block these signals far more effectively than lower-frequency waves. In many cases, signals cannot reliably pass from one room to another. Furniture, equipment, and even people can interrupt transmission. A single obstruction in the signal path can break the link. This sensitivity makes them poorly suited for environments where movement and change are constant.
For example, Wireless HDMI can conveniently connect computers to monitors and TVs. Its 60 GHz signals are typically limited to in-room deployments and often require beamforming. This high-frequency application provides ample bandwidth but struggles to consistently establish and maintain a connection due to how signals at those frequencies attenuate and how even transient obstructions, such as a person walking between the transmitter and receiver, can interrupt the connection. They must often fall back to the lower 2.4 GHz or 5 GHz frequencies for stability at the expense of bandwidth.
Why Indoor Environments Are Especially Challenging
Most sensitive data and critical systems reside indoors, often behind multiple physical barriers. High-frequency wireless signals struggle in these settings.
Unlike lower frequencies that can spread and reflect throughout a building, high-frequency signals often require precise alignment and minimal obstruction. Maintaining this alignment over time is difficult, especially in offices, labs, and industrial facilities where layouts change, and people move frequently.
The combination of limited transmit power, faster decay, and an inability to penetrate physical objects makes them inefficient at exfiltrating data from an indoor location to the outside. These constraints make it extremely difficult to use high-frequency wireless links for hidden communication inside buildings.
Satellite Internet and Satellite Phones in Context
Satellite communications frequently appear in discussions of wireless risk because they connect directly to infrastructure outside traditional networks. Services such as satellite internet and satellite phones operate at higher frequencies and seem like an easy way to move data in or out of a facility.
In reality, satellite systems come with clear limitations. They require an unobstructed view of the sky to work properly. Inside buildings, satellite signals degrade dramatically or stop working altogether unless an external antenna is part of the transmission path. Even portable satellite phones often struggle indoors and may only work near windows or outdoors.
Satellite terminals and antennas are also difficult to conceal. They require visible hardware, stable placement, power, and sometimes permanent mounting. Something as relatively small as a Starlink terminal is still visible. Installing and operating this equipment inside controlled or secure environments increases the likelihood of detection. Satellite phones are larger than typical mobile phones and come equipped with big external antennas, making covert use difficult.
A 2024 U.S. Navy investigation provides a real-world example of these dynamics in action. Senior enlisted personnel aboard the USS Manchester secretly installed a consumer Starlink satellite internet terminal so a small group could access the Internet at sea, bypassing official restrictions. They installed the terminal on a pallet on the ship’s weather deck, but the Navy discovered the covert installation. The senior chief responsible was later demoted after a court-martial, in part because unauthorized satellite communications posed security and operational risks to the vessel.
Challenges, Cost, Complexity, and Risk
For an attacker, stealing data or maintaining remote access requires a dependable connection. High-frequency wireless links make this problematic.
Short range, sensitivity to obstacles, and environmental variability undermine reliability. Satellite connections introduce additional uncertainty due to changing satellite positions, weather conditions, and network management beyond the attacker’s control.
When more dependable options exist, attackers rarely choose technologies that increase the chance of disruption or exposure.
High-frequency wireless equipment is more expensive and requires greater technical expertise. Specialized radios, antennas, and careful setup increase both expense and effort. The lack of hardware available on the market, especially at a reasonable cost, makes this frequency range limited to more sophisticated attackers who can afford it.
From an attacker’s perspective, this complexity provides only a slight advantage compared to standard off-the-shelf hardware. Lower-frequency devices cost less, work more reliably indoors, and require far less expertise to deploy. The added cost of high-frequency systems makes them unattractive for most scenarios.
Sophisticated Adversaries Face the Same Limits
Well-funded adversaries, including nation-state actors, have access to advanced tools. However, they cannot avoid the fundamental physical limits of radio waves.
High-frequency signals still degrade quickly, are susceptible to physical obstructions, and are limited in transmission power, especially if covert communications are the goal. Operations that rely on visible equipment or close proximity increase operational risk and reduce flexibility.
As a result, even advanced adversaries tend to favor techniques and equipment that offer reliability and concealment over theoretical performance. By operating in crowded frequency bands, such as the 2.4 GHz and 5 GHz bands, attackers can hide their activities within the environment’s noise, making them difficult to identify.
Even documented incidents involving advanced attackers indicate a reliance on COTS hardware because it is cheap, easy to use, simple to acquire, reliable, and can hide in plain sight.
One such example involved a wireless breach at a financial services firm, where attackers used a COTS drone and a Wi-Fi Pineapple. The attackers mounted the Wi-Fi Pineapple to the drone and flew it onto the organization’s rooftop, then conducted an Evil Twin attack, successfully breaching and persisting in the network. The security team eventually found the gear on the rooftop after identifying a duplicate MAC address on the network, but they could not determine how long it had been there.
Wireless threats overwhelmingly operate below 7 GHz because these frequencies offer the best balance of range, coverage, affordability, and availability. Devices in these bands are commonplace and blend seamlessly into everyday environments.
This reality holds across industries, from corporate offices to research facilities and industrial sites.
Bastille’s View on High-Frequency Wireless Risk
From Bastille’s perspective, effective wireless security focuses on how attackers operate in practice rather than on what is technically possible. Real-world observation consistently shows that meaningful risk concentrates in frequency ranges that support reliable indoor operation and long-term use.
Bastille provides continuous, 100% passive monitoring across the frequency ranges where practical threats occur. While Bastille can also assess higher-frequency activity through spectrum surveys and extended frequency coverage, these capabilities primarily support confirmation and assurance rather than day-to-day threat detection.
Signals above 7 GHz, and especially those above 30 GHz, face physical, operational, and economic barriers that sharply limit their usefulness for covert compromise. Consumer satellite communications follow the same pattern, requiring visible infrastructure and clear-sky access, which increases detectability.
By grounding wireless security in real-world behavior and physical realities, Bastille helps organizations focus on the threats most likely to affect their environments and avoid overestimating risks that rarely materialize.


