Emerging Tech: Security — The Need for Wireless Airspace Cybersecurity
Download now▶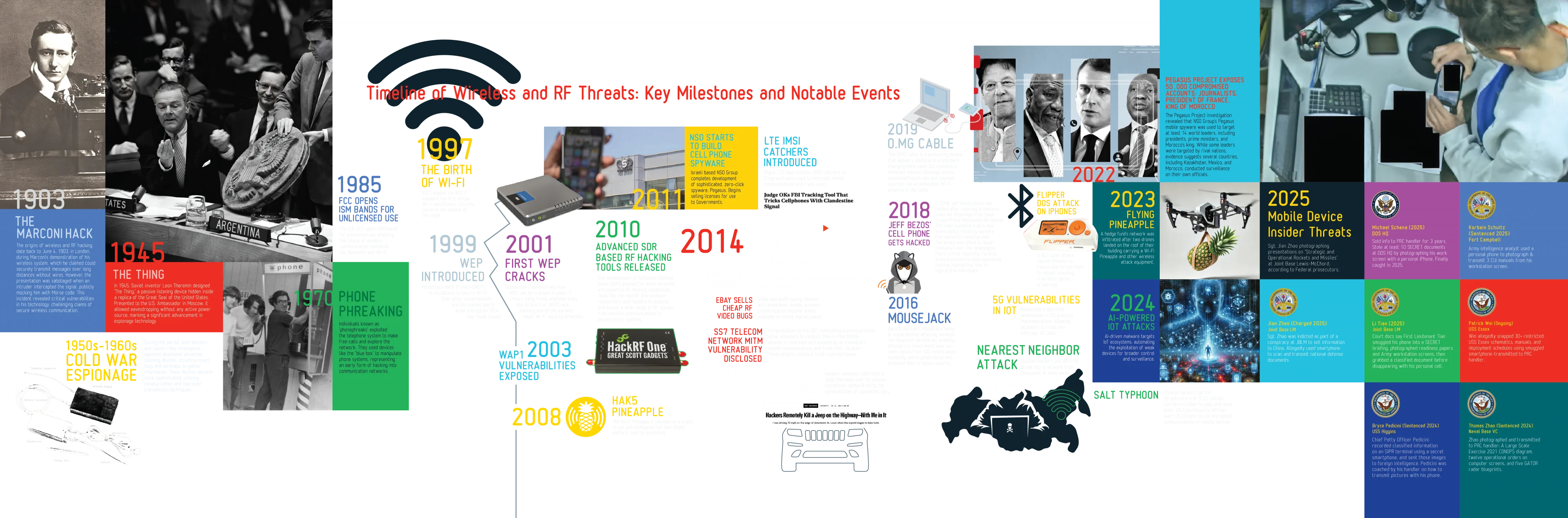
Timeline of Wireless & RF Threats: Key Milestones and Notable Events
2026
AirSnitch
A suite of attacks released in February 2026 by Mathy Vanhoef and collaborators (presented at NDSS'26) that breaks Wi-Fi client isolation — the feature meant to stop guest-network users from reaching the main network. AirSnitch demonstrates three classes of bypass: abusing shared GTK group keys to inject packets to any client, "gateway bouncing" to route traffic through the router at the IP layer, and cross-BSSID port stealing to intercept uplink and downlink traffic.
The result: man-in-the-middle attacks are restored against most home routers and many enterprise networks, even with WPA2/3 encryption enabled.
Coruna
A powerful iOS exploit kit (also known as CryptoWaters) disclosed by Google's Threat Intelligence Group on March 3, 2026, containing five full exploit chains and 23 individual exploits targeting iPhones running iOS 13.0 through 17.2.1. Originally developed in part by Trenchant — a unit of U.S. defense contractor L3Harris — Coruna proliferated from commercial surveillance customers, to a suspected Russian espionage group targeting Ukrainian users, and finally to cybercriminals running watering-hole attacks from fake Chinese financial websites.
CISA added three of its CVEs to the Known Exploited Vulnerabilities catalog, and Apple issued emergency patches for iOS 15 and 16 to protect older devices.
WhisperPair
A Bluetooth vulnerability (CVE-2025-36911) disclosed in January 2026 by KU Leuven researchers that abuses Google's Fast Pair protocol to hijack headphones from brands like Sony, JBL, Anker, and Jabra within a 14-meter range. In about 10 seconds, an attacker can forcibly pair with a target's headset — even when it's not in pairing mode — then eavesdrop through the microphone, blast audio, or stalk the owner's location via Google Find Hub. iPhone, Mac, Windows, and Linux users are hit hardest, since their unclaimed headsets let attackers register themselves as the legitimate owner.
2025
Researchers Shut Down ICS Electrical Controllers with Flipper Zero
Researchers exploit vulnerabilities in the Radio Ripple Control Protocol used to manage critical electrical facilities in several European countries. Demonstrate several remote radio attacks with a Flipper Zero that can shut down electrical controllers.
New Mirai IoT botnet breaks record with 5.6 Tbps DDOS Attack
A variant of the Mirai botnet, primarily composed of vulnerable routers and wireless cameras sets new record for DDOS attack. IoT and networking devices are a persistent and growing security hole.
119 Vulnerabilites in LTE/5G Implementations Disclosed
119 vulnerabilities in major LTE/5G implementations allow attackers to persistently disrupt all cellular communication across cities. Many attacks can be performed from an unauthenticated cellular device without a SIM card. Attackers with access to a home-use femtocell could perform network core breaches, enabling city-wide surveillance of subscriber locations and connections, targeted attacks on specific users, or manipulating core network infrastructure.
US Army Personell Indicted for Using Personal Phones to Photograph Classified Military Information and Sell it to China
U.S. Army Supply Sergeant Jian Zhao & 1st Lt. Li Tian, stationed at Joint Base Lewis-McChord were charged with conspiring to obtain and transmit national defense information as well as bribery and theft of government property. The complaint alleges Zhao was recruited into an ongoing conspiracy to transmit classified military documents around July 2024 and continuously conspired to transmit classified information till the date of his arrest in March 2025.
Zhao allegedly used several "end-to-end encrypted messaging applications" to communicate over voice and text with his co-conspirator, former army personell, Ruoyu Duan, and used his personal cellphone to take photos and videos of classified documents, including using a mobile application to scan documents page by page and using his phone to record several videos of his government computer screen. According to court documents, on or about Nov. 28, 2021, and continuing to at least on or about Dec. 19, 2024, Duan and Tian along with others conspired with each other to surreptitiously gather sensitive military information related to the United States Army’s operational capabilities.
Tian was tasked with gathering information related U.S. military weapon systems, including information related to the Bradley and Stryker U.S. Army fighting vehicles, and transmitting them to Duan and allegedly also used his personal phone to photograph information.
State Department Employee Charged with Using iPhone Sent by Chinese State Actors to Photograph Top Secret Information on His Computer Screen at State Department Headquarters
Department of State employee, Michael Schena, was charged for Conspiracy to Gather, Transmit, or Lose National Defense Information. The complaint highlights that Schena had been caught this February when video surveillance allegedly observed him using a white, personal cellphone to take images of multiple documents, which were displayed on the monitor of his classified computer and marked as “SECRET” and then opening an application on his phone and sending these images.
According to court documents, an investigation of Schena's recovered electronic devices and communication records revealed Schena allegedly began illegally selling information to individuals via messaging platforms almost 3 years prior, in April 2022. Schena is alleged to have previously received payment from individuals for photographs and information sent over these platforms at least 12 seperate times since April 2022.
Court documents also allege Schena had received an invoice for the receipt of "an iPhone 14 mobile device from Jason" and "79841 CNY." Investigators believe that CNY is a reference to Chinese Yuan Renmenbi. Schena was immediately arrested outside his home, the same day surveillance footage observed him allegedly photographing his work monitor. Investigators allege he had a white Apple iPhone 14 on his person that was registed to a foreing number, and still contained photographs of the classified documents from his work monitor.
Taiwanese President's Security Guards Convicted of Photographing Intelligence Information with Personal Phones, Selling it to China
Four Taiwanese soldiers, including three from a security unit responsible for the president's office were sentenced to prison for using their personal smartphones to photograph sensitive military documents and transmit this confidential information to Chinese intelligence agents.
Naval Machinist Sentenced to 200 Months for Photographing Naval Secrets
Wei a Navy Machinist, photographed 30+ restricted U.S.S. Essex schematics, manuals, and deployment schedules using his personal smartphone inside various restricted areas and sent them to a Chinese intelligence agent. Was sentenced to 200 months of prison.
A phone defeated the world's leading endpoint vendor.
In November 2025, a CrowdStrike employee took $25,000 to photograph his monitor with a cellphone and send the images to the Scattered Lapsus$ Shiny Hunters group to establish his visual proof of access to internal Crowdstrike systems the attackers wanted access to. The attacker quickly sent over SSO cookies, and this was likely also transmitted using his cellphone used to send his workstation photographs, although this is unconfirmed.
Sinaloa Cartel FBI Phone Hack
Revealed in an August 2025 Department of Justice Inspector General report, this 2018 incident showed how the Sinaloa cartel hired a hacker who staked out the U.S. Embassy in Mexico City and obtained the mobile phone number of the FBI's Assistant Legal Attaché working the El Chapo investigation. Using only that number, the hacker pulled geolocation data and call logs from the agent's phone, then tapped into Mexico City's video-surveillance network to physically track the agent across the capital and identify the informants they met.
That intelligence was reportedly used to intimidate and kill cooperating sources. The case became a landmark example of "ubiquitous technical surveillance" (UTS) — the fusion of commercial ad-tech data, telemetry, and public camera networks — which the FBI has since elevated to a Tier 1 Enterprise Risk and internally described as "existential."
Russian RF Spy Ring
A Russian intelligence spy ring uncovered in 2025 that targeted Ukrainian and U.S. personnel using a sophisticated radio-frequency arsenal assembled almost entirely from commercially available equipment. Operatives deployed software-defined radios, directional antennas, rogue access points, cellular modems, and IMSI catchers — the last used to fingerprint the cellphones of Ukrainian soldiers training at a U.S. military base, so their devices could be tracked back to missile defense positions on the front lines.
Investigators also recovered 495 SIM cards, suggesting heavy use of burner phones and covert cellular uplinks for hidden audio-visual recorders. The case showed that espionage-grade RF surveillance has been democratized, and that defense facilities need real-time spectrum visibility just as they monitor networks and endpoints.
Airoha Bluetooth Headphone Takeover
A trio of vulnerabilities (CVE-2025-20700, -20701, -20702) disclosed by ERNW researchers Dennis Heinze and Frieder Steinmetz in Airoha Bluetooth system-on-chips exposed a custom debug protocol called RACE. Any attacker in Bluetooth range can silently connect without pairing, read and write device memory, extract the cryptographic link key, then impersonate the headset to hijack a connection to the paired smartphone. 29 models across Sony, Bose, JBL, Marshall, Jabra, Beyerdynamic, JLab, Teufel, and Xiaomi were confirmed vulnerable.
Full technical details and an attack toolkit were released at 39C3 on December 27, 2025.
PerfektBlue
Four chained Bluetooth vulnerabilities (CVE-2024-45431 through -45434) in OpenSynergy's BlueSDK stack, disclosed July 2025 by PCA Cyber Security, enable one-click remote code execution on vehicle infotainment systems. OpenSynergy states BlueSDK ships in roughly 350 million vehicles. Researchers demonstrated working exploits against Mercedes-Benz NTG6/NTG7, Volkswagen ID.4 (MEB ICAS3), and Skoda Superb (MIB3) head units, plus a fourth unnamed automaker.
Once inside the infotainment unit, attackers can track GPS, record cabin audio, read phonebooks, and potentially pivot deeper into the vehicle network. OpenSynergy patched in September 2024, but many automakers had still not pushed firmware updates at disclosure.
AirBorne
23 vulnerabilities (17 CVEs) disclosed April 29, 2025 by Oligo Security researchers Uri Katz, Avi Lumelsky, and Gal Elbaz in Apple's AirPlay protocol and SDK. Chaining CVE-2025-24252 with CVE-2025-24206 yields zero-click, wormable remote code execution on any macOS device with AirPlay enabled on the local network. CVE-2025-24132 — a buffer overflow in the AirPlay audio SDK — delivers zero-click RCE on third-party speakers and CarPlay units, exposing microphone eavesdropping and vehicle GPS tracking.
The flaws reach 2.35 billion Apple devices, 800+ CarPlay-equipped vehicle models, and tens of millions of third-party speakers. Apple patched in iOS 18.4 and macOS 15.4.
Paragon Graphite
Israeli spyware vendor Paragon Solutions' Graphite tool caught targeting journalists and activists. In January 2025, WhatsApp notified roughly 90 users — journalists and civil-society figures in multiple countries — that they had been hit by a zero-click exploit. In June 2025, Citizen Lab confirmed forensic evidence of Graphite on the iPhones of Fanpage.it Naples editor Ciro Pellegrino and a second unnamed European journalist, both infected via CVE-2025-43200, a zero-click iMessage flaw triggered by a malicious iCloud Link.
Apple patched the bug in iOS 18.3.1 on February 10, 2025. Italy's COPASIR oversight committee confirmed Italian intelligence used Graphite against activists Luca Casarini and Giuseppe Caccia; Paragon subsequently terminated its Italy contracts.
Salt Typhoon Goes Global
Throughout 2025, the China-linked Salt Typhoon telecom-espionage campaign was confirmed to reach far beyond the nine U.S. carriers breached in 2024. The FBI stated in August 2025 that at least 200 organizations across 80+ countries had been targeted, and 600+ organizations were notified of potential compromise. New 2025 victims included satellite operator Viasat, Comcast, Charter (Spectrum), Windstream, Consolidated Communications, Digital Realty, a U.S. state National Guard, Canadian telcos, and providers in Norway, the UK, Italy, and all four Singapore telecoms.
Treasury sanctioned Sichuan Juxinhe Network Technology on January 17, 2025, and the FBI posted a $10 million bounty in April 2025. The group continued exploiting CVE-2023-20198 in Cisco IOS XE edge routers.
UN General Assembly SIM Farm
On September 22-23, 2025, days before the UN General Assembly, the U.S. Secret Service dismantled a network of SIM-box servers hidden across five sites within a 35-mile radius of UN headquarters in New York City. Investigators recovered 300+ SIM servers and more than 100,000 active SIM cards — capable of sending 30 million text messages per minute, disabling cellular service across New York City, and routing anonymous threats to senior U.S. officials.
The Secret Service described the operators as nation-state-linked and said the investigation began after a wave of imminent telecommunications threats earlier in 2025. Firearms and 80 grams of cocaine were also recovered at the sites.
Satelite IP Network Vulnerability
UC San Diego and University of Maryland researchers Wenyi Zhang, Annie Dai, Keegan Ryan, Dave Levin, Nadia Heninger, and Aaron Schulman used an $800 off-the-shelf satellite dish on a San Diego rooftop to passively scan geostationary satellite traffic over three years. They found roughly half of GEO satellite IP links are transmitted with no encryption. In just 9 hours of T-Mobile backhaul, they collected 2,700 U.S. phone numbers and unencrypted call and text content.
They also intercepted AT&T Mexico and Telmex voice calls, U.S. military vessel communications, Mexican military and law-enforcement traffic, Walmart Mexico corporate email, SCADA data from oil pipelines and power utilities, and bank data from Santander, Banorte, and Banjército
SS7 Phone Communication TCAP Bypass
Threat intelligence firm Enea disclosed in July 2025 that an unnamed Middle Eastern commercial surveillance vendor had been actively exploiting a novel SS7 bypass technique since late 2024. The attack manipulates extended tag encoding on the TCAP layer to slip past carrier SS7 firewalls, then issues location queries that resolve a target's phone to within a few hundred meters. The technique was being used against real subscribers on live networks when Enea identified it.
It joins a string of 2025 disclosures reminding operators that the global signaling backbone — designed in the 1970s — remains exploitable despite a decade of firewall investment.
ESP32 Hidden Bluetooth Commands
In March 2025 Tarlogic researchers Thierry Joulin and Matúš Potoček disclosed CVE-2025-27840: 29 undocumented Host Controller Interface commands hidden in the Bluetooth stack of Espressif's ESP32, a Wi-Fi/Bluetooth chip shipped in more than 1 billion IoT devices. One command (0xFC02) writes arbitrary memory, enabling device spoofing, persistent backdoors, and pivoting onto networks the chip is connected to.
Espressif disputed the original "backdoor" framing, arguing the commands are proprietary debug functionality living in the Bluetooth spec's vendor-reserved opcode range, but committed to an SDK update to remove them. The disclosure highlighted the long tail of hidden functionality lurking in low-cost connectivity silicon.
BadBox 2.0
A supply-chain infection impacting more than 10 million low-cost Android Open Source Project devices — off-brand TV boxes, projectors, tablets, digital picture frames, and car infotainment units — pre-loaded with backdoors before leaving Chinese factories. Infected devices joined a global residential-proxy and ad-fraud botnet. The FBI issued public service announcement I-060525-PSA on June 5, 2025, warning consumers.
On July 11, 2025, Google filed suit in the Southern District of New York against 25 Chinese entities allegedly behind the operation.
Kimwolf Botnet
In late 2025 Chinese security firm XLab documented Kimwolf (operated by the same group behind AISURU): a botnet of roughly 1.8 million infected Android TV boxes. Between November 19 and 22, 2025, Kimwolf issued 1.7 billion DDoS commands in just three days. Command-and-control hides on the Ethereum blockchain using an "EtherHiding" technique — bots resolve the ENS domain pawsatyou.eth to a smart contract that returns the current C2 address, making takedowns nearly impossible.
The botnet supports 13 distinct DDoS methods and represents a new generation of IoT botnets that piggyback on decentralized infrastructure to defeat traditional disruption.
MU-MIMO Precoding Attack
At IEEE INFOCOM 2025 in London, a team led by Francesco Restuccia at Northeastern University presented a Wi-Fi attack exploiting a design flaw in 802.11 MU-MIMO precoding: by injecting crafted frames, a nearby attacker can force an access point to allocate the weakest beamforming to a chosen victim, slowing or degrading their connection on demand while leaving everyone else alone. The paper won Best Paper Award.
Crucially, the flaw is in the standard itself, not an implementation bug, so it cannot be fixed in already-deployed Wi-Fi 6 and Wi-Fi 7 hardware — a correction must wait for Wi-Fi 8.
Tesla Model 3 UWB Relay Attack
In 2025 Chinese security team GoGoByte demonstrated a relay attack against Tesla Model 3 keyless entry that uses ultra-wideband radio. UWB was introduced in phones and cars specifically because, used correctly, it resists the signal-relay tricks that have haunted Bluetooth and low-frequency key fobs. But Tesla's implementation does not use UWB's secure distance-bounding mode — so with under $100 of equipment, researchers relayed the signal between a parked car and an owner's phone hundreds of meters away, opened and drove off.
Tesla's PIN-to-drive feature blocks the final step but is not enabled by default.
CAN Invader Toyota Thefts
Through 2025, "CAN Invader" devices — CAN-bus injection tools disguised as JBL-style Bluetooth speakers and sold on dark-web forums — became the dominant method for stealing popular keyless vehicles. Thieves pry the wheel-arch liner or front bumper to reach CAN wiring at the headlight connector, plug in the device, inject forged "key present" messages, and drive off in under two minutes. Toyota RAV4, Highlander, Land Cruiser, C-HR, and Corolla Hybrid are the marquee targets, along with Lexus RX and NX, parts of the VW MQB platform, and some Ford and BMW models.
Canada logged more than 2,000 RAV4 thefts in 2024 and the trend accelerated sharply through 2025; factory immobilizers and Faraday pouches offer no protection.
2024
Pakistan APT used Hak5 Wireless Pentesting Devices to Infiltrate Indian Gov Buildings
Researchers disclose that a Pakistan Gov linked APT had been using Hak5 devices to communicate large amounts of data from an Indian Ministry of Foreign Affairs office in Europe, an Indian national defense organization, and several other government bodies to a remote Hak5 branded C2 server. Russian APT eventually conmpromised this server for its own cyber operations.
"Hi My Name Is Keyboard" Bluetooth Keystroke Injection Attack
Bluetooth vulnerabilities in modern Android, Linux, macOS, iOS and Windows can be exploited to pair an emulated Bluetooth keyboard and inject keystrokes without user confirmation. No patches are available for older MacOS, iOS, or Android operating systems.
Kali Nethunter Incorporates "Hi My Name Is Keyboard" Automatic Bluetooth Vulnerability Scanning and Ducky Exploit Scripts
Kali Nethunter, a smartphone based wireless pentesting application, expands Bluetooth vulnerability scanning, automates exploitation of Bluetooth pairing vulnerability that leads to 0-click code execution
Kali Nethunter Adds Wi-Fi Pumpkin3 Evil Access Point capabilities
Kali Nethunter adds Wi-Fi Pumpkin3 toolkit, allowing sophisticated evil access point attacks via mobile devices. Now supports over 100 different mobile devices
Novispy Zero-Click Android Spyware Exploiting Several Qualcomm Zero days reported
Serbian government reported to infect phones of activists and reporters with Novispy spyware. Researchers believe the attacks use zero day exploits in the Qualcomm chips that allow device infection via the Android Calling function.
Spyloan Android Malware Infects 8 Million Users
A dozen apps on the Google app store containing hidden Android Spyware are reported to have infected over 8 million users. The malware had continued to evade detection by Google Play.
Joint Cybersecurity Advisory Warns Russian SVR's Exploiting 3 Bluetooth Vulnerabilities
Joint Western Intelligence Agencies issue advisory warning Russian SVR's are exploiting 3 wireless vulnerabilities alongside traditional attacks.
Canada Bans 'Flipper Zero' SDR
Canadian Government bans the Flipper Zero SDR device to combat spate of RF based car-jacking attacks
Cinterion Modem SMS RCE Vulnerabilities
Kaspersky disclosed a severe vulnerability to millions of industrial devices using the cellular Cinterion IoT Modem. Attackers could send malicious SMS messages to these devices to remotely execute arbitrary code and perform unauthorized privelege escalation
Salt Typhoon
Chinese Hackers tap the infrastructure of 9 US Cellular Carriers to listen to calls and steal texts. US Cybersecurity officials warn US citizens to use encrypted communications on mobile devices.
Nearest Neighbor Attack
Russian Hackers use Wi-Fi to break into a network from thousands of miles away
The Russian hacking group, APT 29, puts Zero Click Spyware on watering hole websites.
The Russian-based APT29 group was seen using the same iOS and Google Chrome exploits as commercial surveillanceware vendors NSO Group and Intellexa, in an espionage campaign that targeted the Mongolian government. Researchers do not know how Russian actors gained access to these vulnerabilities.
AI-Powered IoT Attacks
AI-driven malware targets IoT ecosystems, automating the exploitation of weak devices for broader control and surveillance.
NSA Warns All iPhone and Android Users Should Restart Phone Every Week. Turn off Bluetooth.
The National Security Agency (NSA) has recommended that all iPhone and Android users restart their devices at least once a week and to make sure Bluetooth is turned off. The agency states restarting mobile devices can help disrupt the operations of malware and other malicious software that may have infiltrated the system.
Wireless Transmitter Implant in Three-Stars General Name Tag
Chinese spies planted a surveillance chip in a former U.S. three-stars general’s conference name tag to observe him during his time serving in the Indo-Pacific.
Bryce Pedicini
Chief Petty Officer Pedicini recorded Classified information on an SIPR terminal using a secret smartphone, and sent those images to a foreign intelligence service. Pedicini was coached by his handler on how to transmit pictures with his phone.
2023
US Army Warns of Mysterious Smartwatches Mailed to Servicemembers: Auto-Connecting to Wireless Networks and Devices
Service members across the military have reported receiving smartwatches unsolicited in the mail. These smartwatches, when used, have auto-connected to Wi-Fi and began connecting to cell phones unprompted, gaining access to a myriad of user data.
Flipper DoS Attack on iPhones
A BLE spam attack caused iPhones to freeze and forced them to reboot, creating a wireless denial of service
Triangulation Attack: iPhones infected by malicious iMessage
Kaspersky researchers reported iPhones had been infected with spyware via malicious iMessages that exploited hardware registries in the device that Apple's firmware did not know existed. The device owner would not see they had received a malicious message and the device could be reinfected at any time by receiving another malicious iMessage.
Roaming Mantis Android Malware Spreads via Wirelessly Compromising nearby Wi-Fi routers
The Roaming Mantis campaign was reported to spread its mobile malware to other devices via compromising nearby Wi-Fi routers (e.g., using DNS changers to redirect Android users to malicious servers, distributing Wroba.o malware to steal credentials or hijack devices. Initially targeting South Korean routers, the attack has spread globally as infected devices connect to new networks.
Flying Pineapple
A hedge fund's network was infiltrated after two drones landed on the roof of their building carrying a Wi-Fi Pineapple and other wireless attack equipment
Predator demonstrates Pegasus-like zero click Spyware Capabilities
Predator can intercept communications, activate device sensors, and exfiltrate data. The attack chain shares architectural similarities with other zero-click exploits like Pegasus, but uses chains focused on browser components rather than messaging apps. Predator has recently been reported to have restored its infrastructure and operates in over 11 countries.
5G Vulnerabilities in IoT
Researchers identified weaknesses in 5G protocol implementations, allowing attackers to track and intercept IoT data.
2022-2023
US Army Intelligence Analyst Used Personal Phone to Film and Transmit Classified Information to China
Korbein Schultz, a U.S. Army intelligence analyst, plead guilty to charges of conspiring to unlawfully obtain and transmit national defense information to a foreign national. From approximately June 2022 through October 2023, Schultz used personal phones and encrypted messaging platforms to transmit classified information and communicate with "Conspirator A," based in Hong Kong. Conspirator A advised Schultz on secure communication methods, specifically intstructing him "to get a new phone and to set up a new account with a foreign electronic messaging application" to transmit files securely.
Conspirator A directed Schultz to collect sensitive military information in return for payment. Schultz took photographs of confidential documents and photographs of his computer screen using his personal phone and transmitted them to Conspirator A over encrypted messaging applications. The information Schultz sent included technical manuals for the HH-60W helicopter, F-22A fighter aircaraft, and intercontinental ballistic missile systems.
2022
Researchers Discover iPhone can be infected with malware via Bluetooth while powered off
Researchers discover that Low Power Mode for the 'Find My' functionality of the Bluetooth Chip allows UWB, NFC and Bluetooth chips to access the phone's secure element when powered off. They demonstrate that attackers could install malware on the Bluetooth chip that can infect the device while it is powered off.
Pegasus Project exposes 50,000 compromised accounts: journalists, President of France, King of Morocco
The Pegasus Project investigation revealed that NSO Group's Pegasus mobile spyware was used to target at least 14 world leaders, including presidents, prime ministers, and Morocco's king. While some leaders were targeted by rival nations, evidence suggests several countries, including Kazakhstan, Mexico, and Morocco, conducted surveillance on their own officials.
FragAttacks on Wi-Fi
Fragmentation and Aggregation Attacks (FragAttacks) expose vulnerabilities in Wi-Fi implementations, affecting devices from multiple vendors.
2021-2023
U.S. Navy Personell Used Personal Cellphones to Film and Photograph Classified Military Information & Sell it to China
In 2021-2023, two U.S. Navy servicemen—Jinchao Wei (aka Patrick Wei) and Wenheng Zhao (aka Thomas Zhao)—were indicted for conspiring with a Chinese intelligence officer (identified as "Conspirator A") to transmit sensitive U.S. military information to the People's Republic of China in exchange for payments. Wei, a Machinist's Mate on the USS Essex amphibious assault ship, and Zhao, a Construction Electrician in Naval Mobile Construction Battalion 3, are alleged to have used "multiple internet-based encrypted methods to communicate" with Conspirator A.
Beginning in February 2022, Wei allegedly took photographs and videos of the USS Essex via his personal phone, including its weapons systems and potential vulnerabilities, and transmitted these materials through secure communication applications as instructed by Conspirator A, who told Wei to "send photographs and other material obtained through his service in the U.S. Navy through a particular secure communication application." Similarly, Zhao allegedly photographed sensitive military materials using his personal phone, including "12 photographs of computer screens that displayed operational orders of military training exercises" and "five photographs of diagrams and blueprints outlining the electrical system" of radar systems at a U.S. military base in Okinawa.
Both men were instructed to "destroy evidence regarding the nature of their relationship and their activities" and received regular payments from Conspirator A totaling approximately $14,866.76 (for Zhao) and at least $15,000 (for Wei) between November 2021 and March 2023.
2021
BlueJacking: A hijacking attack against Bluetooth-enabled devices
Bluejacking is a form of wireless exploitation that takes advantage of Bluetooth technology's device discovery capabilities. The attack occurs when a malicious actor sends unsolicited messages or files to nearby Bluetooth-enabled devices that have their visibility set to "discoverable." The vulnerability exists due to Bluetooth's inherent device pairing process and limited range security controls.
BrakTooth exposes billiions of devices to Bluetooth vulnerabilities
Researchers discover “BrakTooth,” a series of vulnerabilities in 13 manufacturer's SoC chip Bluetooth stacks that allow attackers to execute code, crash devices, or disrupt connections. The vulnerabilities affected billions of devices across critical industry, IoT, Automobile manufacturing, and consumer electronics. Several manufacturers announced they would not release patches, or would only patch vulnerable devices on request.
LTE Layer Attacks
Researchers discovered that attackers could exploit vulnerabilities in LTE networks to track devices and intercept calls or data.
IoT Ransomware Emerges
Hackers began targeting IoT devices like smart thermostats and cameras with ransomware attacks.
2020
Zigator Toolkit Released
This Zigbee attack suite includes functions for impersonating devices, disconnecting devices, leaking credentials, conducting reconnaissance, MitM attacks, and more
Phillips Hue Smart Bulbs Allow Network Compromise Over Zigbee Vulnerability
Researchers discovered a vulnerability (CVE-2020-6007) in Philips Hue smart bulbs that allows hackers to infiltrate networks through installing malware on the device through the ZigBee protocol. The malware then connects back to the hacker, who can use known exploits and vulnerabilities to enable IP network infiltration and malware propagation
BlueSmacking: A denial of service attack against Bluetooth-enabled devices
BlueSmacking is a denial-of-service attack against devices that exploits the L2CAP protocol ping mechanism. Attackers can overwhelm targeted device's resources by sending oversized ping packets via Bluetooth and potentially cause system crashes. The Kali Nethunter app allows certain android phones to conduct these attacks on any nearby Bluetooth devices.
Sweynetooth
The SweynTooth vulnerability family consists of 12 BLE vulnerabilities affecting multiple IoT device manufacturers. These flaws allow attackers within radio range to cause device crashes, deadlocks, and security bypasses. Millions of devices are vulnerable to these attacks, including smart home devices, fitbits, and medical devices.
Bluetooth BlueFrag Android Vulnerability
A critical Bluetooth vulnerability (CVE-2020-0022) affected Android 8.0-9.0 devices, allowing remote code execution without user interaction when Bluetooth was enabled. Android 10 was partially affected.
Ripple20 Vulnerabilities
Discovered in the Treck TCP/IP stack used by IoT devices, Ripple20 allowed remote code execution on millions of devices.
IoT Worm Attacks
Botnets like Mozi targeted IoT devices with weak security to spread malware and launch DDoS attacks.
2019
Large scale SS7 Attacks on Mobile Banking Users
Bank acccounts around the world are reported to be hacked by cybercriminal groups using SS7 vulnerabilities to intercept 2-factor authentication codes.
O.MG Cable
The O.MG Cable is a pentesting device that appears identical to a standard charging/data cable but contains a malicious implant allowing remote automated keystroke and payload injection via an embedded wi-fi antenna in the cable.
Wi-Fi Dragonblood
Vulnerabilities in WPA3 are discovered, dubbed “Dragonblood,” exposing flaws in the new Wi-Fi security standard. The vulnerabilities affected billions of Wi-Fi enabled devices, and allowed attackers to downgrade connections, perform side-channel attacks, and potentially extract network passwords.
BLE Spoofing
Researchers demonstrated spoofing attacks on Bluetooth Low Energy (BLE) devices, compromising secure connections and allowing attackers to inject spoofed data into the device. The vulnerabilities were reported to affect up to one billion Linux, Android, and iOS devices, worldwide
Trend Micro Identifies Severe RF Vulnerabilities in ICS Equipment
The research identified several attack vectors that can be executed within 300 meters range (or several kilometers with signal amplifiers). Affected devices include tower cranes, industrial cranes, and mobile hoists.
2018
Department of Homeland Security Identifies Rogue IMEI Catchers in DC
DHS says it has observed "anomalous activity" consistent with Stingrays in the Washington area.
GRU Agents Conduct Wi-Fi Attacks in Netherlands
Four GRU agents were apprehended after conducting Wi-Fi attacks in the Netherlands
BTLEJack Toolkit Released
Bluetooth attack suite for sniffing, jamming, and/or hijacking BLE networks
Jeff Bezos' cell phone gets hacked
In 2018, Jeff Bezos's phone was hacked after receiving a malicious video via WhatsApp from Saudi Crown Prince Mohammed bin Salman. The video exploited a zero-day vulnerability, installing spyware that extracted sensitive data. The attack was linked to Saudi retaliation over The Washington Post’s critical reporting. Forensic analysis pointed to state-sponsored hacking, highlighting risks to high-profile individuals.
NASA JPL Wireless Implant Hack
A cybersecurity audit revealed that an attacker had managed to wirelessly exfiltrate data out of NASA's Jet Propulsion Laboratory, undetected for over 10 months. The attacker used a raspberry pi they had connected directly to network infrastructure at the laboratory which they remotely controlled via a wireless conection to the device.
SirenJack
Bastille discovered SirenJack, a vulnerability in ATI Systems' emergency sirens, allowing remote activation via unencrypted radio signals, risking false alarms and public panic.
Dark Vishnya Malicious Wireless Implant Attack on European Banks
Kaspersky reports a series of 8 seperate attacks on European banks where attackers used malicious hardware implants that they direclty connected to bank networking routers. The devices had embedded cellular modems which attackers used to remotely access the implants and eventually infiltrate the bank's inner network. Estimated losses are $8 million
Bluetooth KNOB Attack
Key Negotiation of Bluetooth (KNOB) attack is revealed, exploiting weaknesses in Bluetooth’s key negotiation process to intercept encrypted communication. The KNOB attacks affected Bluetooth chips from 17 different manufacturers, impacting over a billion devices worldwide.
LTE Protocol Exploits
Researchers identified flaws in LTE protocols, enabling impersonation attacks, eavesdropping, and tracking.
Amazon Echo and Alexa Exploited
Security researchers used ultrasonic waves to exploit IoT voice assistants, forcing them to execute unauthorized commands.
2017
BlueBorne Bluetooth Vulnerability
Researchers identified a series of vulnerabilities potentially affecting an estimated 5.3 billion Bluetooth devices that allow attackers to compromise devices without Bluetooth pairing or approval. The Researchers created a botnet of infected devices using the BlueBorne attack vector as a worm to infect other nearby Bluetooth devices.
KRACK Attack on WPA2
The Key Reinstallation Attack (KRACK) exploits vulnerabilities in WPA2 protocol, allowing attackers to intercept, decrypt and manipulate Wi-Fi traffic.
2016
MouseJack
Bastille discovers MouseJack family of vulnerabilities affecting wireless non-Bluetooth peripherals, enabling attackers to inject keystrokes via radio signals from 100 meters away, exploiting unencrypted mouse and keyboard data to bypass security.
KeyJack
Bastille discovers the KeyJack vulnerability, allowing attackers to send encrypted keystrokes to be injected into a vulnerable wireless keyboard’s dongle without knowledge of the encryption key.
Mirai Botnet
Mirai exploited weak or default passwords in IoT devices, forming a massive botnet used in DDoS attacks.
2015
Chrysler Jeep Hack
Hackers remotely controlled a Jeep Cherokee over its cellular connection, demonstrating the vulnerabilities of connected cars.
2014
Ebay sells cheap RF Video Bugs
Video and audio spying devices with embedded remote wireless communication become widely available on online marketplaces.
Bastille Networks Founded
Former ISS security experts, SDR specialists from Georgia Tech, and alumni of the DARPA Spectrum Challenge joined forces to establish Bastille Networks in Atlanta, Georgia.
Heartbleed Vulnerability
This OpenSSL bug impacted many IoT devices, exposing sensitive data in wireless communications.
SS7 Telecom Network MiTM Vulnerability Disclosed
Vulnerabilities to the SS7 telecomunications protocol allow attackers to conduct Man-in-The-Middle attacks to intercept and eavesdrop on individual's mobile communications and track their location. These attacks continue to be reported today.
2013
Bluetooth PIN Brute Force
Researchers demonstrated brute-force attacks against Bluetooth pairing, exposing weaknesses in PIN-based pairing mechanisms.
2012
Mexico Pays $20MM for Pegasus Subscription
The Mexican Government purchases license for Mobile Zero-Click Spyware, Pegasus. It eventually becomes largest reported user of the software.
2011
NSO starts to build Cell Phone Spyware
Israeli based NSO Group completes development of sophisticated, zero-click spyware, Pegasus. Begins selling licenses for use to Governments.
Wi-Fi WPA2 Vulnerabilities
Researchers demonstrate flaws in WPA2 networks, including weak password implementations.
LTE IMSI Catchers Introduced
Rogue LTE base stations (IMSI catchers or Stingrays) were used to intercept mobile communications and track users.
2010
Advanced SDR based RF Hacking Tools released
The development of Software-Defined Radio (SDR) allowed for more versatile and powerful RF hacking capabilities. Tools like the HackRF One enabled researchers and hackers to analyze and exploit a wide range of RF signals, from satellite communications to keyless entry systems.
Bluetooth BlueBugging
“BlueBugging” becomes a recognized threat, allowing attackers to gain control of devices via Bluetooth to make calls or send messages.
Stuxnet Malware
Stuxnet exploited vulnerabilities in industrial control systems, including wireless IoT protocols, to sabotage Iran’s nuclear facilities.
2008
Wi-Fi Evil Twin Attacks
“Evil Twin” attacks gain traction, where attackers set up rogue access points to mimic legitimate networks and intercept user data.
Hak5 pineapple
The Wi-Fi Pineapple is released as a simple to use, pre-configured Evil Twin Attack platform, sold for pentesting.
RFID Cloning Exploits
Researchers successfully cloned RFID tags, compromising security systems reliant on this technology.
ATM Wireless Hardware Supply Chain Compromise
Credit card readers used in UK supermarkets had a wireless device inserted in them by the manufacturer in China. The device copied a credit card when inserted, and transfered the information via a Wi-Fi connection to Lahore, Pakistan. Estimated losses were $50 million.
BeSeLo: Bluetooth + MMS Worm
Researchers discovered a new Bluetooth and MMS worm attacking mobile phones running on the S60 software platform. Similar to CommWarrior, the worm spread via MMS and then to any nearby devices within Bluetooth range.
ZigBee Vulnerabilities
ZigBee, a popular protocol for IoT devices, was found to have weak key management, enabling attackers to hijack IoT devices.
2005
Bluetooth BlueSnarfing
“BlueSnarfing” is discovered, where attackers can exploit Bluetooth to steal data from nearby devices without user consent.
CommWarrior: Bluetooth + MMS Worm
The CommWarrior worm exploited MMS and Bluetooth vulnerabilities in mobile devices running on the Nokia S60 platform to spread and steal information from the device. Over 100,000 devices were discovered to be infected by CommWarrior.
2004
Cabir Bluetooth Attack: 1st Mobile Device Worm
Kaspersky researchers reported on the first worm affecting mobile devices. Cabir would attempt to infect all nearby Bluetooth devices that accepted the Object Push Profile, which included SymbOS mobile devices, some laptops, and some printers.
2003
WAP1 vulnerabilities exposed
2001
Maroochy Shire Wastewater SCADA Radio Attack
A disgruntled SCADA engineer issued over 2,000 radio commands to radio controlled pumping stations around Maroochy Shire, Australia. Over the course of several months he released over 1,000,000 gallons of raw sewage throughout the area. The engineer was caught with radio equipment in his truck that he had been using to remotely control the pumps.
First WEP Cracks
Researchers demonstrate how WEP can be cracked in under 2 hours using freely available tools like AirSnort or WEPCrack, marking one of the earliest major Wi-Fi security breaches.
2000
Bluetooth and RFID Vulnerabilities
The widespread adoption of Bluetooth and RFID technologies introduced new attack vectors. Hackers demonstrated the ability to exploit vulnerabilities in these wireless protocols to gain unauthorized access to devices and data.
1999
WEP Introduced
Wired Equivalent Privacy (WEP) is introduced to secure Wi-Fi. Soon after, vulnerabilities are discovered due to weak encryption (RC4 key reuse issues).
1997
The Birth of Wi-Fi
IEEE releases the 802.11 standard, the first official Wi-Fi specification. Security concerns are minimal at this stage.
1991
First GSM Networks Launched
Vulnerabilities in the GSM encryption algorithm (A5/1) were later exploited, allowing attackers to intercept and decrypt GSM communications.
1990
Wireless Network Exploitation
As wireless networks became more prevalent, hackers began exploiting weaknesses in Wi-Fi security protocols. Tools were developed to intercept and decrypt wireless communications, leading to increased awareness of the need for robust wireless security measures.
IEEE begins development of the 802.11 standard
IEEE begins development of the 802.11 standard, which would eventually become Wi-Fi.
1985
FCC Opens ISM bands for unlicensed use
The U.S. FCC opens ISM bands for unlicensed use, enabling the future of wireless communication standards like Bluetooth and Wi-Fi.
1980
1980s Computer and Wireless Hacking Emergence
The rise of personal computers led to the emergence of computer hacking. In 1988, the Morris Worm became one of the first widely recognized computer worms, disrupting numerous systems and highlighting vulnerabilities in network security.
1970
Phone Phreaking
Individuals known as "phone phreaks" exploited the telephone system to make free calls and explore the network. They used devices like the "blue box" to manipulate phone systems, representing an early form of hacking into communication networks.
1950-1960's
1950s-1960s: Cold War Espionage
During this period, both Western and Eastern bloc intelligence agencies developed advanced listening devices, including covert bugs and wiretaps, to gather information. These devices became more sophisticated, utilizing miniaturization and improved transmission techniques.
1945
The Thing
In 1945, Soviet inventor Leon Theremin designed "The Thing," a passive listening device hidden inside a replica of the Great Seal of the United States. Presented to the U.S. Ambassador in Moscow, it allowed eavesdropping without any active power source, marking a significant advancement in espionage technology.
1903
The Marconi hack
The origins of wireless and RF hacking date back to June 4, 1903, in London, during Marconi's demonstration of his wireless system, which he claimed could securely transmit messages over long distances without wires. However, the presentation was sabotaged when an intruder intercepted the signal, publicly mocking him with Morse code. This incident revealed critical vulnerabilities in his technology, challenging claims of secure wireless communication.
Last Updated: 2026-04-20
Request a Demo
See how the most advanced wireless airspace cybersecurity solution provides 24/7 visibility and protection for your critical infrastructure.
