Recent reports surrounding a French naval officer’s use of a fitness application underscore a broader, more urgent reality for defense, intelligence, and critical infrastructure leaders. The modern threat environment is shaped not only by cyber intrusions but by the persistent collection and correlation of wireless, commercial, and open-source data.
In the reported incident, publicly shared fitness data may have enabled observers to estimate the location of the French aircraft carrier Charles de Gaulle in the Mediterranean. Whether viewed as an isolated lapse or a representative example, the lesson is clear. Routine activity conducted through an RF-emitting consumer device can create operationally relevant intelligence.
This issue is not simply a privacy problem. It is a modern surveillance problem.
The Rise of Ubiquitous Technical Surveillance
Ubiquitous Technical Surveillance, or UTS, defines today’s operating environment. Individuals, devices, and facilities are persistently observable through overlapping layers of data exhaust that include:
- RF emissions from smartphones, wearables, laptops, and Bluetooth accessories
- GPS and mobile application telemetry
- Public social media and open source reporting
- Commercial location and ad-tech data
- Cloud synchronization and third-party data aggregation
Taken individually, these signals may appear insignificant. When correlated over time, they can reveal identity, movement, pattern of life, location, associations, and intent.
That is what makes UTS so consequential for national security. The threat no longer depends on sophisticated intrusions against secure networks. A near-peer adversary can exploit ordinary technical signatures and commercially available data to build actionable intelligence without ever breaching a protected system.
Why Wireless Devices Create Persistent Exposure
Wireless devices are always producing information. Even when they are not actively in use, they emit signals and metadata that adversaries can observe, log, and analyze.
Smartphones, fitness devices, tablets, laptops, and Bluetooth accessories continuously advertise their presence, attempt to establish connections, exchange identifiers, and connect to cloud services. Applications synchronize data in the background, devices broadcast telemetry, and external platforms collect and store that information.
The result is a persistent and exploitable stream of digital exhaust.
For adversaries, this means a single fitness upload, Bluetooth signal, or advertising identifier can become the starting point for broader analysis. Open-source research, satellite imagery, commercial datasets, social media, and observed RF activity can then be fused to identify high-value personnel, infer patterns of behavior, and expose sensitive operational activity.
Correlation Is the Real Risk
The most important point for leaders to understand is that the risk is not any single signal. The risk arises from the correlation among multiple signals across time and sources.
A wearable device can reveal movement, while an application can reveal location. An advertising identifier can expose behavioral history, and a public profile can link that activity to identity. An RF signature can confirm continued presence inside a sensitive environment.
When combined, these fragments can identify a senior Government leader, expose the location of a sensitive facility, map a mission pattern, or reveal the location of a military asset.
In the hands of a near-peer adversary, this becomes a low-cost, scalable intelligence collection model.
Why This Matters Beyond the Maritime Domain
While the reported French case involved a naval platform, the underlying issue is far broader.
Government facilities, defense installations, SCIFs, SAPFs, laboratories, data centers, manufacturing environments, and corporate campuses all face the same underlying challenge. Employees, contractors, and visitors carry multiple unmanaged wireless devices into sensitive spaces every day. Many of those devices continuously emit RF signals and exchange data with external services.
Most organizations still focus primarily on the network. That creates a significant operational security blind spot and provides near-peer adversaries with an opportunity to fingerprint an organization, an employee, or mission dynamics, or to predict activity based on their collected patterns of life.
If an organization cannot observe what is operating in its RF environment, it cannot determine which devices are present, whether those devices are authorized, how they are behaving, or whether they are creating exploitable exposure that adversaries can correlate outside the perimeter.
Bastille’s Role in Closing the Visibility Gap
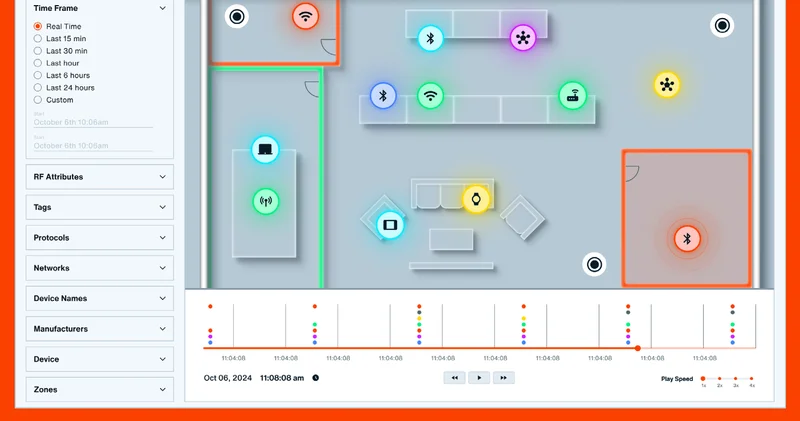
Bastille addresses this challenge by delivering persistent visibility into the wireless environment itself.
Using 100 percent passive monitoring, Bastille detects and analyzes RF activity without transmitting, thereby preventing the near-peer adversary from fingerprinting the organization, interfering with operations, or relying on participation from the managed network. The platform allows security teams to identify wireless devices operating within their environment, classify activity, distinguish authorized from unauthorized presence, and investigate behavioral anomalies.
That matters because organizations cannot defend against what they cannot see.
In a world shaped by UTS, Bastille helps security teams detect device activity and wireless signatures that traditional security tools miss. This capability reduces the risk that adversaries will collect and correlate RF emissions, application telemetry, open-source exposure, or commercial data exhaust and use it against the organization.
The Strategic Takeaway
The lesson from incidents like this is straightforward. National security exposure does not begin only when an adversary penetrates a network. It can begin with a wearable device, a mobile application, a persistent RF signature, or a stream of commercial data linked to the wrong person in the wrong place at the wrong time.
That is the operational challenge created by Ubiquitous Technical Surveillance.
For defense, intelligence, and critical infrastructure organizations, the requirement is clear: gain visibility into the wireless environment, understand the signals and devices operating within it, and reduce the technical signatures that adversaries can collect and correlate.
Bastille provides that visibility and, with it, the ability to better protect mission, personnel, and national security.