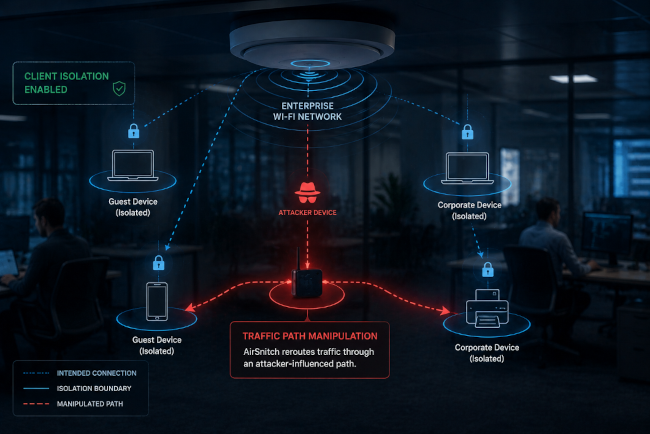
AirSnitch is a wireless infrastructure attack technique that exposes weaknesses in enterprise Wi-Fi client isolation by manipulating traffic forwarding behavior in enterprise wireless networks. The research challenges long-standing assumptions around segmentation, isolation, and enterprise wireless security.
Introduction
Client isolation prevents devices connected to the same Wi-Fi network from communicating directly with one another.
Security teams rely on it to limit lateral movement and enforce separation across shared infrastructure. Combined with WPA2 or WPA3 encryption, it has served as a foundational control in enterprise wireless security.
That assumption is no longer reliable.
New research from Palo Alto Networks Unit 42 introduces AirSnitch, a wireless infrastructure attack technique that bypasses Wi-Fi client isolation by manipulating traffic forwarding behavior.
Encryption still protects data in transit. AirSnitch does not target encryption. It targets the path traffic takes, allowing attackers to interact with communications in ways isolation controls should prevent.
For enterprise environments, this changes the risk model.
For years, organizations treated wireless isolation as an infrastructure guarantee rather than a security condition that required continuous validation. AirSnitch challenges that assumption by showing that isolation depends not only on policy, but also on how infrastructure behaves under adversarial conditions.
The question is no longer just whether devices can communicate directly. It is whether attackers can influence communication paths to weaken isolation boundaries inside the network.
Why This Should Be a Wake-Up Call for Enterprises
AirSnitch matters because it challenges one of the most common assumptions in enterprise Wi-Fi design: that guest users and internal users remain safely separated as long as client isolation and encryption are enabled.
In many enterprise environments, organizations intentionally design guest Wi-Fi networks to be simple and accessible. Organizations often deploy open or minimally protected guest networks with only a splash page or basic terms-of-service acknowledgment. Security teams typically accept this model because they assume isolation controls prevent guest users from interacting with protected clients or sensitive traffic.
AirSnitch raises new concerns around guest Wi-Fi isolation in enterprise environments, where organizations often assume that logical separation alone is enough to prevent interaction between untrusted and internal systems.
In many enterprises, guest Wi-Fi networks exist in the same physical environment as corporate systems, employee devices, and sensitive applications. Organizations rely on segmentation and client isolation to maintain separation between those environments. AirSnitch challenges the assumption that separation always behaves as expected.
The Unit 42 research suggests that attackers may be able to influence how traffic moves across wireless infrastructure in ways that weaken those isolation boundaries, even when:
- Client isolation remains enabled
- WPA2 or WPA3 remains intact
- Segmentation policies appear correctly configured
AirSnitch does not mean attackers automatically gain unrestricted access to internal networks. It means the underlying trust model around wireless separation may not behave as expected under real-world conditions.
For enterprises, that should be a significant concern.
Many organizations treat guest Wi-Fi as low risk because they logically separate it from production systems. AirSnitch demonstrates that logical separation alone may not fully account for how wireless infrastructure behaves at lower layers.
That shifts the conversation from “Is the network segmented?” to “Can the infrastructure reliably maintain separation under adversarial conditions?”
The issue is no longer just network access. It is whether wireless isolation boundaries hold when attackers influence traffic paths themselves. Understanding how AirSnitch manipulates those traffic paths helps explain why traditional isolation assumptions may no longer hold.
How AirSnitch Bypasses Wi-Fi Client Isolation
AirSnitch does not turn off client isolation. It works around it. Instead of enabling direct communication, it subverts the path traffic takes, weakening isolation without breaking policy.
Unit 42 researchers showed it can influence:
- Client associations with access points
- Traffic forwarding decisions
- Client traffic forwarding paths
These effects rely on low-level infrastructure manipulation techniques, including MAC spoofing and traffic forwarding manipulation.
By influencing these interactions, an attacker can position themselves within the communication path between devices that should remain isolated, enabling:
- Potential indirect interception between clients
- Potential packet manipulation within active sessions
- Traffic redirection through attacker-influenced paths
Client isolation remains configured, but AirSnitch reduces its effectiveness. Client isolation enforces separation. AirSnitch weakens how that separation is maintained.
Why Encryption Alone Does Not Protect Wireless Isolation
Encryption and client isolation solve different problems. WPA2 and WPA3 protect data confidentiality. Client isolation prevents interaction between devices. AirSnitch operates between them.
It assumes:
- Encryption remains intact
- Isolation policies remain in place
Then it targets how traffic moves, creating a gap:
- Data stays encrypted
- Isolation appears enforced
- The communication path becomes untrusted
Encryption supports isolation, but it does not guarantee it.
Why Enterprise Wi-Fi Security Assumptions Are Changing
Enterprise wireless security has traditionally relied on layered assumptions:
- Encryption protects data
- Segmentation separates networks
- Client isolation prevents interaction
AirSnitch challenges the assumption that these controls always work together as expected.
The issue is not that the controls disappear. The issue is that attackers may influence how the infrastructure applies those controls in practice.
Organizations have historically treated wireless isolation as an invisible trust layer inside enterprise environments. AirSnitch demonstrates that this trust layer may be more fragile than they assumed.
Why Detection Is Difficult
Most enterprise tools validate isolation at the policy level:
- Segmentation rules
- Access controls
- Endpoint visibility
AirSnitch operates below that layer.
Because it interacts with RF signals and Layer 2 behavior, it can:
- Preserve the appearance of isolation
- Avoid triggering policy violations
- Appear as normal encrypted traffic
Isolation can appear intact while attackers reduce its effectiveness.
Key Takeaways
- AirSnitch targets Wi-Fi infrastructure behavior rather than encryption
- WPA2 and WPA3 remain intact during the attack
- Client isolation may not fully prevent adversarial interaction
- Infrastructure traffic forwarding becomes part of the wireless attack surface
- Enterprise wireless visibility becomes critical for detecting abnormal behavior
Where Bastille Fits
Enterprise wireless security requires visibility beyond traditional network telemetry. Bastille supports wireless threat detection through continuous visibility into RF activity and wireless infrastructure behavior, helping organizations validate whether wireless isolation boundaries behave as expected under real-world conditions.
Through 100% passive monitoring, organizations can:
- Observe device interactions
- Identify unexpected wireless activity
- Analyze patterns that may indicate how networks maintain wireless separation between clients
In path-based scenarios, this visibility can:
- Provide context around device associations
- Surface anomalies in wireless interactions
- Support investigation when traditional logs are insufficient
Bastille complements encryption and client isolation by adding visibility into how they operate in real conditions.
The Bottom Line
AirSnitch exposes a limitation in how client isolation is understood. Client isolation enforces policy. Encryption protects data. Neither guarantees that devices remain effectively isolated.
AirSnitch shifts the focus to how organizations maintain isolation through infrastructure behavior. Security teams must look beyond configuration. Behavior matters.
Isolation depends not only on rules, but on how those rules operate in practice.
Learn how Bastille provides continuous visibility into wireless infrastructure behavior to help organizations detect abnormal activity and strengthen enterprise wireless security.
FAQ
Does WPA3 stop AirSnitch?
No. AirSnitch does not target encryption directly. It targets traffic forwarding behavior within wireless infrastructure.
Can client isolation still fail when segmentation is enabled?
Research suggests attackers may still influence communication paths even when segmentation and isolation policies remain active.
Why is wireless visibility important?
Traditional security tools may not detect lower-layer wireless infrastructure behavior that affects isolation boundaries.

