AI-enabled wearable technologies, including Meta’s smart glasses, are moving from early adoption to widespread use. These devices combine cameras, microphones, onboard sensors, and cloud-connected artificial intelligence, often through a paired smartphone, to provide hands-free access to information, real-time assistance, and contextual support. As adoption increases, organizations that operate sensitive environments face growing security, privacy, and compliance challenges that traditional controls do not fully address.
Public attention around AI-enabled glasses continues to increase. Recent news coverage of Meta’s legal proceedings and executive testimony highlighted the company’s strong push to position AI glasses as a primary interface for AI assistants. The reporting underscored how wearable AI devices embed sensing capabilities and internet-enabled connectivity through a paired phone into everyday use, raising broader concerns about privacy, data collection, and the real-world surveillance implications. In one report, a judge admonished Meta personnel for wearing Meta glasses in a courtroom that prohibited recording devices, reinforcing concerns about recording capabilities in environments governed by strict privacy rules.
These public incidents and policy responses illustrate how AI-enabled wearables intersect with established security controls.
In early 2026, the U.S. Air Force updated its uniform policy to prohibit the use of Meta AI smart glasses while in uniform. The Air Force cited operational security concerns, including unintended audio and video capture and the risk of data processing or storage outside approved government systems. Although other military services have not implemented identical restrictions, this policy decision reflects growing awareness of the risks posed by AI-enabled wearables in controlled environments.
Organizations across government, defense, critical infrastructure, healthcare, research, and regulated enterprise settings now face similar challenges as these devices proliferate.
The Growing Risk Profile of AI Smart Glasses in Sensitive Environments
AI-enabled smart glasses introduce distinct risks that complicate oversight, policy enforcement, and operational security.
Discreet, Hands-Free Recording in Restricted Spaces
Smart glasses allow users to capture audio and video with minimal visible interaction. The glasses can record photos and short videos locally, even when not actively connected to a smartphone, and store them for later transfer. This capability means a device that can capture sensitive content within a restricted environment and store it locally.
A user can later reconnect the glasses to a paired phone and upload or process the recorded content externally. This delayed transmission model increases risk because organizations may not detect any live connectivity at the time of recording.
In sensitive environments, this capability increases the likelihood of inadvertent recording of confidential discussions, proprietary processes, operational workflows, or facility layouts. Even without malicious intent, discreet capture capabilities elevate the risk of accidental exposure of sensitive information.
Ambient-Capable Sensing and Awareness Challenges
AI wearables rely on microphones, cameras, and sensors to support AI-driven functionality. Depending on configuration and user behavior, these sensors can capture background conversations, visible documents, whiteboards, screens, and movement patterns within controlled spaces.
Organizations must address not only intentional recording but also the presence of ambient-capable sensing functionality in environments where awareness, consent, and confidentiality are at issue.
External Data Processing and Data Handling Considerations
Advanced AI features often depend on cloud-based services. When paired with a smartphone, smart glasses can transmit captured data for AI processing or storage over the phone’s internet connection.
This dynamic introduces uncertainty around data residency, retention practices, third-party access models, and alignment with internal governance or regulatory requirements. For organizations operating under strict operational security frameworks, even the possibility of external processing may conflict with internal policy.
Bluetooth Pairing and Indirect Cellular Connectivity Risks
Meta smart glasses typically use Bluetooth to connect to a paired smartphone rather than operating as fully independent cellular devices. The smartphone then provides internet access through its own network connections, including cellular data.
This connectivity model introduces additional risk in sensitive environments. A wearable device may appear to function locally, while the paired phone enables external communication paths outside enterprise monitoring. Organizations must consider the combined risk posed by the glasses and the associated mobile device, particularly when personal phones are either inside or in proximity to restricted zones.
Security teams must account for scenarios in which smart glasses transmit data indirectly via a phone’s cellular connection, thereby bypassing corporate Wi-Fi controls and limiting the effectiveness of network-based policy enforcement.
Bluetooth-Specific Detection and Enforcement Challenges
Bluetooth connectivity presents unique operational challenges in controlled environments. Smart glasses maintain persistent pairing with mobile devices, allowing data transfer without requiring direct interaction with enterprise infrastructure.
Unlike traditional network-based controls that monitor authenticated Wi-Fi sessions, Bluetooth connections often operate outside enterprise visibility. A device may automatically pair upon entering the range of its associated smartphone, establishing a continuous wireless link without requiring access to a corporate network.
In restricted facilities, this behavior complicates enforcement in several ways:
- A user can introduce both the wearable and the paired smartphone into a controlled area.
- The glasses can rely on the phone’s cellular data connection for external communication.
- Security controls focused exclusively on Wi-Fi access may not detect active Bluetooth activity.
- Manual device screening may identify the phone but overlook the wearable.
Organizations that restrict recording or wireless transmission in sensitive areas must address Bluetooth activity as a distinct and persistent wireless exposure vector.
Unmanaged Wireless Activity and Expanded RF Exposure
AI smart glasses operate as wireless devices, typically using Wi-Fi and Bluetooth connectivity. Many of these devices do not authenticate with enterprise networks, nor appear in approved device inventories.
This reality creates wireless blind spots and increases RF exposure in sensitive environments. Security teams that rely only on network access controls may miss unauthorized or unmanaged devices operating near sensitive assets.
Insider Threat and Unauthorized Device Introduction
Wearable AI devices introduce new considerations for insider threats. A user can introduce consumer-grade sensing and connectivity into restricted environments that traditional security controls cannot detect.
Organizations must account for unauthorized recording, the capture of proprietary workflows, and the presence of wireless devices in prohibited zones, without relying solely on user disclosure.
Policy Enforcement Limitations in High-Throughput Facilities
Organizations frequently rely on acceptable use policies or restricted-device zones to manage wearable risk. Small, personal devices complicate enforcement, particularly in environments with visitors, contractors, shared spaces, and high daily device turnover.
Manual screening does not scale and does not provide continuous validation. Organizations require technical visibility to verify compliance in real time.
Compliance and Reputational Impact
Unauthorized recording or sensing can create downstream consequences beyond immediate security exposure. These consequences include privacy concerns, loss of intellectual property, contractual violations, regulatory scrutiny, and reputational damage.
AI-enabled wearables amplify these risks by combining sensing, connectivity, and AI-driven interpretation in a single consumer device.
How Bastille Helps Organizations Address AI Wearable Risk
Bastille adds a dedicated wireless security layer that provides visibility, detection, and context across the RF spectrum. Bastille operates with 100 percent passive monitoring and does not transmit, interfere with, or disrupt wireless communications.
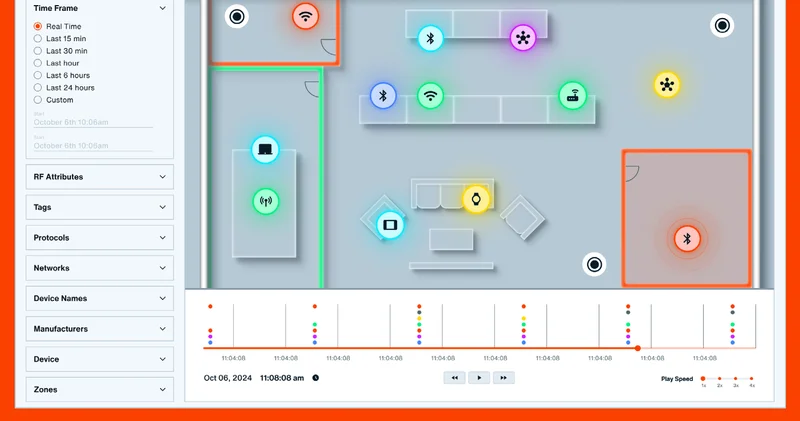
Continuous Visibility Across the Wireless Environment
Bastille continuously monitors wireless activity across a broad range of frequencies, from 100 MHz to 6 GHz, including Wi-Fi up to 7.125 GHz. This visibility enables security teams to identify which devices operate in sensitive environments, including AI-enabled wearables that emit Wi-Fi or Bluetooth signals. Bastille detects devices even when they do not connect to enterprise networks.
Detection of Unauthorized and Unmanaged Devices
Bastille identifies and classifies devices based on their RF characteristics and behavior. This capability allows organizations to detect consumer wearables that fall outside approved inventories or appear in restricted areas. Security teams gain objective insight into device presence without relying on visual inspections, badge checks, or user disclosure.
Patented Localization Algorithms and Analysis for Contextual Response
Bastille applies patented localization algorithms and analysis to provide context on the locations of wireless devices relative to sensitive assets and controlled spaces.
This capability enables security teams to assess proximity, prioritize responses, support investigations, and coordinate with facilities and security personnel.
Policy-Driven Alerting and Security Operations Integration
Organizations define policies that align with acceptable use rules and risk tolerance. Bastille generates alerts when wireless activity violates those policies and integrates with existing security operations workflows to support timely investigation and response.
Support for Risk Management and Compliance Oversight
Bastille provides documented visibility into wireless activity over time. This data supports internal risk assessments, security reviews, and compliance reporting by demonstrating active monitoring of wireless exposure in sensitive environments.
Wireless Visibility as a Requirement in the Age of Wearable AI
AI-enabled smart glasses reflect a broader shift toward ambient computing, in which devices sense, analyze, and connect in response to user interaction and configuration. Organizations should assume these devices will appear in environments that may pose unacceptable risk.
The U.S. Air Force’s restriction on Meta AI smart glasses highlights the importance of pairing policy decisions with technical controls that provide real-world visibility.
Bastille supports this approach by delivering continuous awareness of wireless activity and identifying unauthorized devices in sensitive areas. In environments where unauthorized recording or data transmission could have operational, legal, or safety consequences, wireless visibility is a foundational component of modern security.